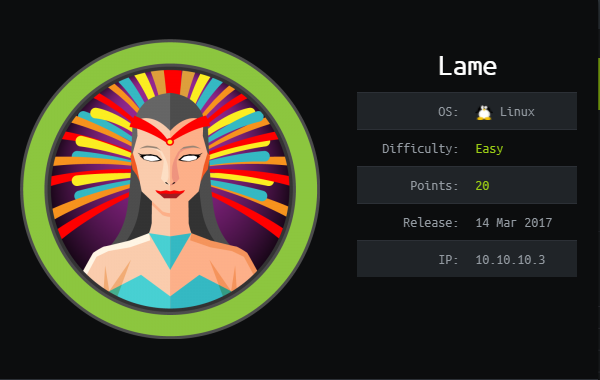
HackTheBox Lame
Enumeración System IP: 10.10.10.3 Matriz de la maquina Esta matriz nos muestra las características de explotación de la maquina. Enumeración de servicios Server IP Address Ports Open 10.10.10.3 TCP: 21,22,139,445,3632 Nmap Scan Resultados: Usando el siguiente comando para enumerar las versiones y servicios que corren en cada puerto luego de hacer un escaneo de puertos abiertos. nmap -A -n -Pn -p21,22,139,445,3632 10.10.10.3 Host discovery disabled (-Pn). All addresses will be marked 'up' and scan times will be slower. Starting Nmap 7.91 ( https://nmap.org ) at 2021-08-28 21:12 EDT Nmap scan report for 10.10.10.3 Host is up (0.12s latency). PORT STATE SERVICE VERSION 21/tcp open ftp vsftpd 2.3.4 |_ftp-anon: Anonymous FTP login allowed (FTP code 230) | ftp-syst: | STAT: | FTP server status: | Connected to 10.10.14.2 | Logged in as ftp | TYPE: ASCII | No session bandwidth limit | Session timeout in seconds is 300 | Control connection is plain text | Data connections will be plain text | vsFTPd 2.3.4 - secure, fast, stable |_End of status 22/tcp open ssh OpenSSH 4.7p1 Debian 8ubuntu1 (protocol 2.0) | ssh-hostkey: | 1024 60:0f:cf:e1:c0:5f:6a:74:d6:90:24:fa:c4:d5:6c:cd (DSA) |_ 2048 56:56:24:0f:21:1d:de:a7:2b:ae:61:b1:24:3d:e8:f3 (RSA) 139/tcp open netbios-ssn Samba smbd 3.X - 4.X (workgroup: WORKGROUP) 445/tcp open netbios-ssn Samba smbd 3.0.20-Debian (workgroup: WORKGROUP) 3632/tcp open distccd distccd v1 ((GNU) 4.2.4 (Ubuntu 4.2.4-1ubuntu4)) Service Info: OSs: Unix, Linux; CPE: cpe:/o:linux:linux_kernel Identificación de vulnerabilidades Como podemos observar, en el puerto 445 corre la version 3.0.20 de samba, entonces hacemos una búsqueda en searchsploit con el comando searchsploit samba 3.0.20. ...
